Plan for E-Mail Migration - SlideShare.
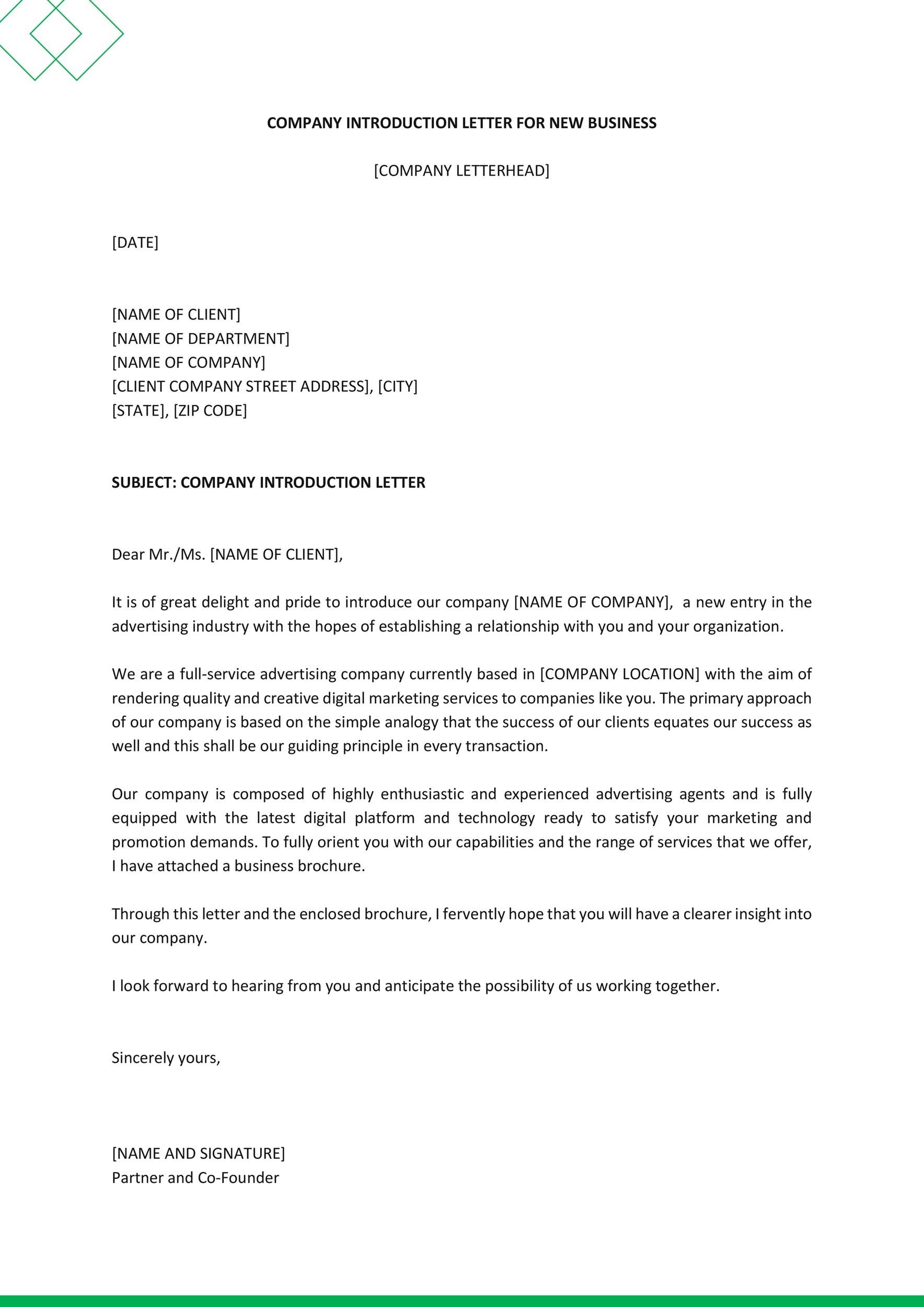
The basic for all good PAC files start with a clear and concise coding methodology. It’s possible to achieve the same result using several different methods, both with the PAC file functions available and the flexibility of the JavaScript language. This page includes a PAC file example which has been proven to be flexible, easy to update.Target operating model (TOM) is a blueprint of a firm’s business vision that aligns operating capacities and strategic objectives and provides an overview of the core business capabilities, internal factors, and external drivers, strategic and operational levers, organizational and functional structure, technology, and information resources of a company.Certain domains are set aside, and nominally registered to “IANA”, for specific policy or technical purposes. As described in RFC 2606 and RFC 6761, a number of domains such as example.com and example.org are maintained for documentation purposes. These domains may be used as illustrative examples in documents without prior.
A 'read' is counted each time someone views a publication summary (such as the title, abstract, and list of authors), clicks on a figure, or views or downloads the full-text.User experience (UX) design is the process design teams use to create products that provide meaningful and relevant experiences to users. This involves the design of the entire process of acquiring and integrating the product, including aspects of branding, design, usability and function.

Whether you need your Ph.D. dissertation written, a simple college essay, an eye-catching PowerPoint presentation, a research paper or an advanced business plan, our fantastic team of highly-skilled writers can help! Your search for the best essay writing service on the market is finally over! At ChiefEssays, we fulfill every request with the.